ATTACK VECTORS
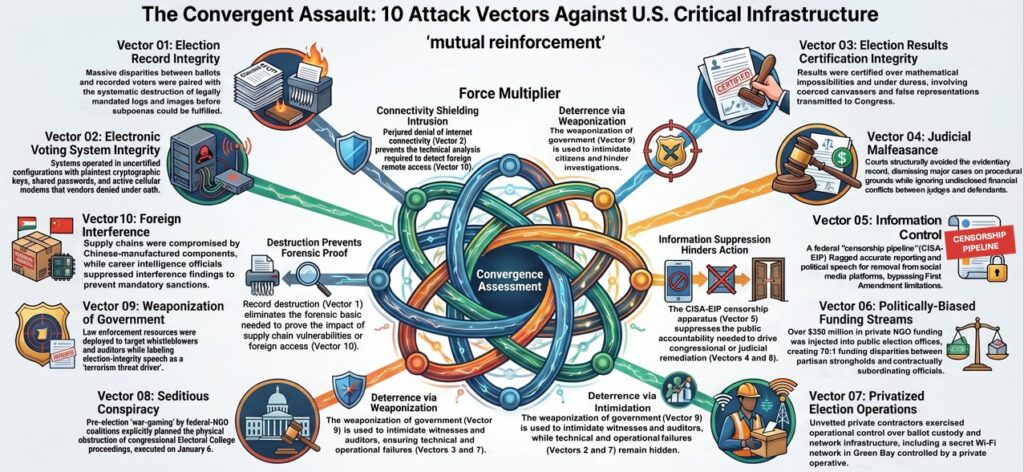
The 2020 general election exposed significant structural vulnerabilities within the American electoral system, concentrated in a small set of battleground states and their core metropolitan counties. This report identifies ten interlocking “attack vectors” (See Figure 5) through which election outcomes can be shaped or shielded from scrutiny: election record integrity, electronic voting systems integrity, election results certification integrity, judicial malfeasance, information control, financial influence, privatized election operations, seditious conspiracy, weaponization of government, and foreign interference.
These ten vectors span every critical layer of election infrastructure: records, systems, certification processes, judicial review, information flows, funding and operations, congressional proceedings, law‑enforcement posture, and foreign access pathways.
The overall subversion of the 2020 election infrastructure would have been materially compromised had any one of the ten vectors not been present. Each vector closes a specific failure mode; its absence would have significantly increased the likelihood that manipulation either could not be executed at scale or could not be successfully concealed.
The evidence in support of each of these attack vectors can be reviewed by clicking on the Attack Vector of interest below.