Executive Summary
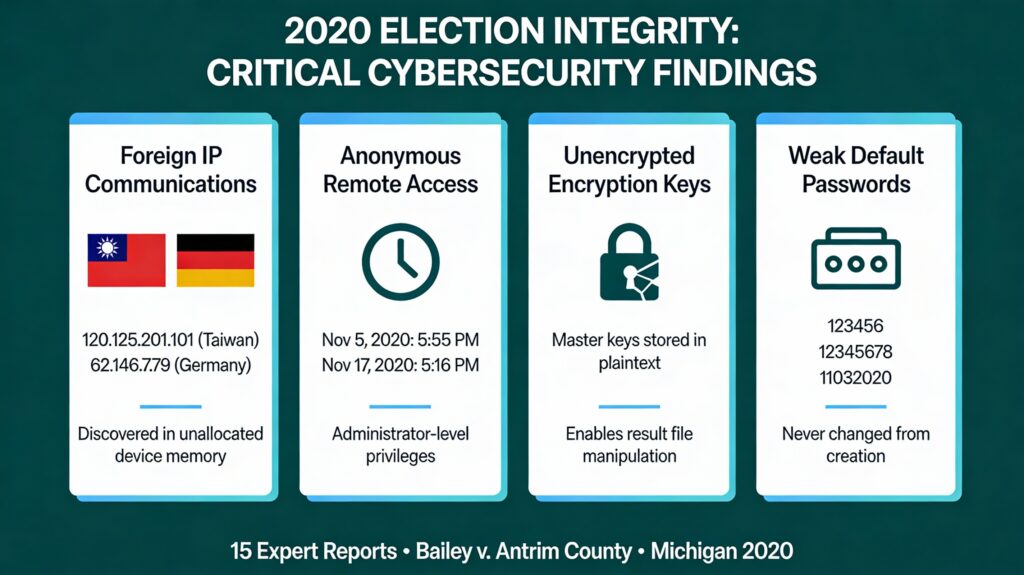
Between December 2020 and June 2021, multiple cybersecurity and forensic experts conducted technical examinations of voting equipment and systems used in Antrim County, Michigan during the November 3, 2020 general election. These examinations, commissioned as part of litigation (Bailey v. Antrim County, Case No. 20-9238-CZ), produced 15 expert reports documenting cybersecurity vulnerabilities, system configuration deficiencies, and anomalous voting patterns that the analysts concluded raised substantial questions about election integrity.
The findings encompass four primary areas of concern:
- critical cybersecurity failures including foreign IP communications and anonymous remote access;
- evidence of what experts characterized as deliberate software manipulation designed to suppress error reporting;
- ballot handling irregularities and physical evidence of tampering; and
- systemic security deficiencies in password management, encryption, and audit logging.
The case was ultimately dismissed by Judge Kevin Elsenheimer based upon the assertion that a statewide audit of the election results had been conducted and not on the basis that the plaintiff did not present compelling evidence of election malfeasance as some have falsely asserted.
I. Critical Cybersecurity Vulnerabilities
A. Network Connectivity and Foreign IP Communications
Forensic examination of a Dominion ImageCast X (ICX) voting device revealed evidence of internet communications to foreign IP addresses, contrary to assertions that voting systems were air-gapped. Benjamin Cotton, founder of CyFIR LLC and a certified forensic examiner with 25+ years of experience, documented these findings in sworn affidavits dated April 8, 2021 and June 8, 2021.
Specific findings:
- Taiwan IP Address: 120.125.201.101, resolving to the Ministry of Education Computer Center in Taipei, Taiwan, was discovered in unallocated space on the ICX device’s 10th partition (physical sector 958273, cluster 106264)
- German IP Address: 62.146.7.79, resolving to a cloud provider in Germany, was found in close proximity to the Taiwan IP address in device memory
- Network Configuration Evidence: The ICX system was actively configured to communicate on private network 10.114.192.x with FTP settings to connect to 10.114.192.12 and 10.114.192.25, and had previously used IP address 192.168.1.50
Cotton concluded these artifacts “definitively identify two things: 1) the device has been actively used for network communications and 2) that this device has communicated to public IP addresses not located in the United States”.
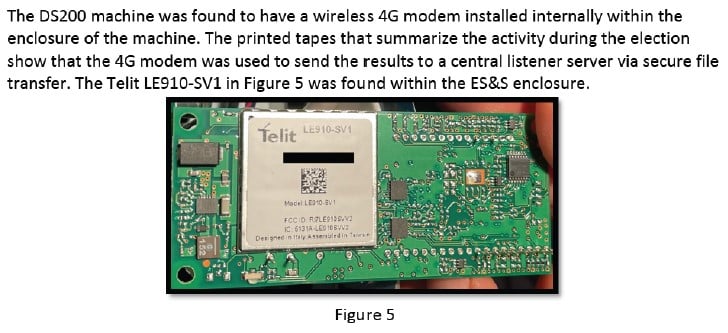
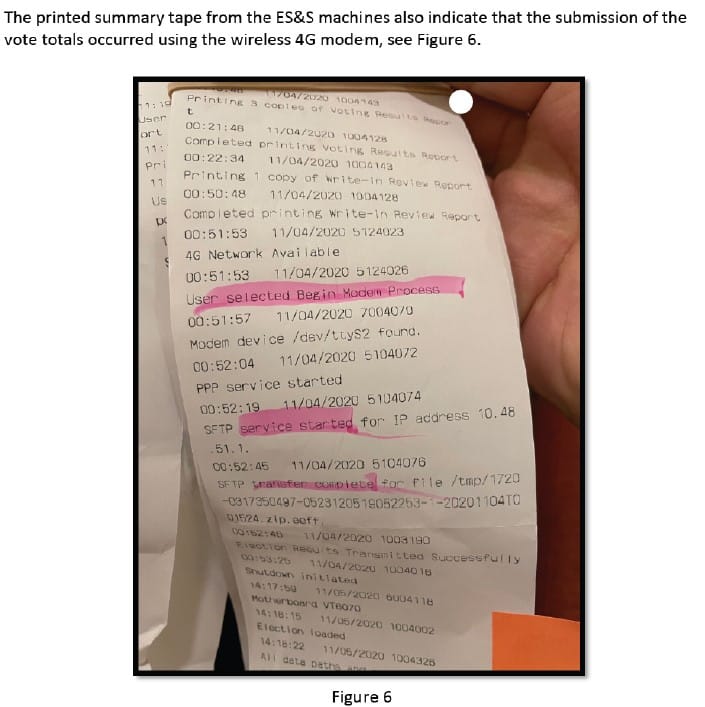
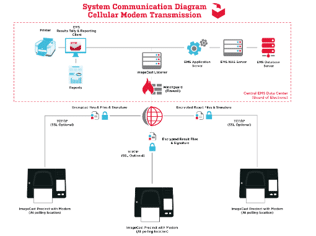
Wireless modem capabilities in ES&S DS200 tabulators were also documented. Each DS200 device contained an active Verizon cellular wireless communications card (Telit LE910-SV1 modem) that powered on automatically with the device. Printed summary tapes confirmed wireless transmission of vote totals via secure file transfer to IP address 10.48.51.1. Testing demonstrated that the SIM card could be removed and used in generic wireless devices to access the same Access Point Name (APN), creating what analysts described as “substantial risk” from unauthorized access.
Dominion Voting Systems itself acknowledged wireless transmission issues in an August 25, 2020 email to Michigan counties: “Modem transmission this election were terrible in some areas! Failures and timing out due to the weaker 3G signal and cellular network issues meant that some of your precincts weren’t able to transmit”. The email also revealed that Dominion “turned off image saving” without authorization from the Secretary of State.
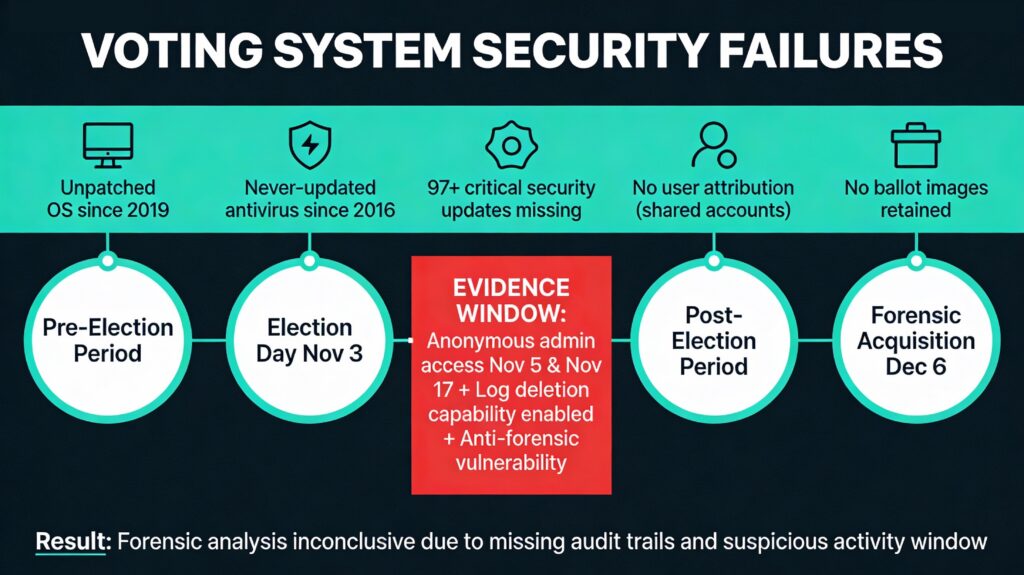
B. Anonymous Remote Administrative Access
The most alarming security breach documented was the discovery of two anonymous remote logins with administrator privileges to the Antrim County Election Management System (EMS) server occurring after the election:
Login Event 1: November 5, 2020 at 5:55:56 PM EST
Login Event 2: November 17, 2020 at 5:16:49 PM EST
Both logins showed escalated privileges at the time of connection. Cotton stated: “Given that this computer was supposed to be on a private network, this is very alarming. One would expect that any network logon, if authorized by the accreditation authority, would require specific usernames and passwords to be utilized, not anonymous users”.
The significance of these dates is magnified by the forensic acquisition timeline:
- November 3, 2020: Election Day
- November 4, 2020: Antrim County officials determine election irregularities exist
- November 5, 2020: First anonymous remote login
- November 6, 2020: Central Lake Township ballot reprocessing
- November 17, 2020: Second anonymous remote login
- November 23, 2020: Motion filed by plaintiff to access election equipment
- December 6, 2020: Forensic acquisition of election equipment
This created a 31-day window between the election and forensic preservation during which analysts noted “cyber attackers frequently employ anti-forensic techniques… to delete or modify system logs and software configurations in order to cover their tracks”. The presence of anonymous administrative access during this period, combined with the deletion of Windows security event logs prior to November 4, 2020, prevented forensic analysts from determining the full extent of unauthorized access.
II. Database Security and Encryption Failures
A. Plaintext Storage of Master Encryption Keys
A critical finding by multiple expert teams was the storage of master cryptographic keys in plaintext within the SQL database. Cyber Ninjas, a cybersecurity firm that conducted application security analysis, documented this in their April 9, 2021 report:
“The master cryptographic key utilized to encrypt all voting results and configuration from the tabulators is stored in plain text in a table within the database for this election. With this key and knowledge about the file formats utilized; it would be possible to alter election results prior to those result files being loaded into the EMS Server, or to alter configurations for the tabulators to make them behave in a certain way”.
The implications extended beyond Antrim County itself. Because ElectionSource (the vendor that created the election project files) was the originator of the database, “any employee at Election Source who had access to the county’s database file, or any nation state that compromised one of their computers; would have the encryption key needed to adjust files on the compact flash cards”.
B. Hard-Coded and Weak Passwords
System analysis revealed pervasive password security failures documented across multiple reports:
Hard-coded credentials compiled into the application itself included the password “dvscorp08!” – unchanged since 2008 and present in multiple program binaries. The Election Assistance Commission had identified this same hard-coded password in a 2010 deficiency report, indicating the problem had persisted for over a decade.
Shared administrative passwords:
- Single password shared across EMSADMIN01, EMSADMIN, EMSUSER, ICCUSER01, ICCUSER02, and emsepsuser accounts
- Two local administrative accounts had no password at all
- Passwords never changed from creation date
Weak default passcodes set by ElectionSource:
- Technician/supervisor passcode: “123456”
- Poll worker passcode: “12345678” (set January 8, 2019, unchanged for 19 months)
- Election day passcode: “11032020” (the date of the election)
Jeffrey Lenberg demonstrated that the technician passcode “123456” enabled poll reopening, time manipulation, and ballot injection without detection. In a controlled test, he successfully:
- Reopened polls after official closure
- Injected additional ballots (demonstrated 4 rounds of 7 ballots each)
- Reset the system time to match original closure time
- Printed new tabulator tapes showing fraudulent “official” timestamps
This capability meant “a malicious election worker/contractor wished to run additional ballots outside of the election window or after hours, the ability to reset the time to print new tapes makes it extremely difficult to identify fraudulent activities”.
C. SQL Database Direct Access Capability
Microsoft SQL Server Management Tools were installed on the EMS server – software not on the Election Assistance Commission’s approved list for certified systems. Combined with Windows SQL Authentication set to “Windows User Mode,” this configuration meant “if an unauthorized user gains access to the system, that unauthorized user would have complete access to the Microsoft SQL server at the level of the compromised user”.
Since all access to the system used the EMSADMIN account (a full administrator), any user could:
- Change vote totals directly in the database
- Add, edit, or delete any user accounts
- Delete logs or audit trails
- Modify any election configuration
Cyber Ninjas concluded: “The Antrim County Election Management System (EMS) environment is setup in a manner where it would potentially be possible for an individual to alter the results of the election without leaving much of a digital trail”.
III. Evidence of Software Subversion
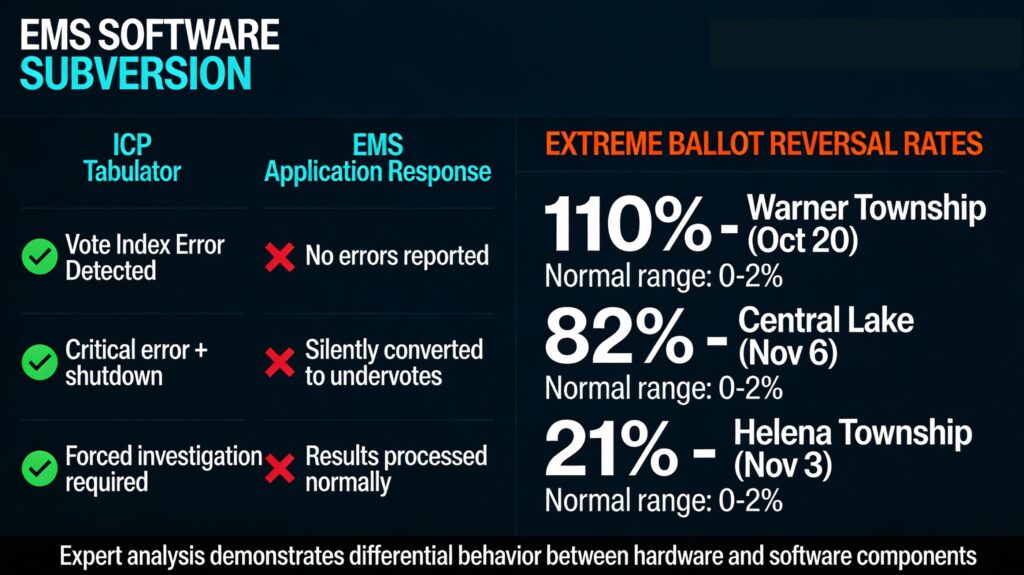
A. Error Handling Manipulation in EMS/RTR System
Perhaps the most technically significant finding was evidence of what analysts characterized as deliberate software subversion designed to suppress critical error messages. Jeffrey Lenberg conducted controlled testing comparing the behavior of ImageCast Precinct (ICP) tabulators versus the Election Management System/Results Tallying and Reporting (EMS/RTR) application when processing manipulated vote data.
Test methodology: Lenberg created a scenario where Biden votes (internalMachineID 3016) were swapped with Natural Law Party straight-ticket votes (internalMachineID 3015), causing vote indexes to cross contest boundaries – a condition that should trigger critical errors.
Results:
| System Component | Response to Vote Index Manipulation |
|---|---|
| ICP Tabulator | – Reported critical error – Refused to process vote file – Did not print paper tape – Wrote error to log file – Forced mandatory shutdown |
| EMS/RTR Application | – No errors reported – Successfully loaded same file – Converted Biden votes to “undervotes” (blank ballots) – Processed and published results normally |
The analysis revealed that the EMS contained “logical bumpers” that prevented vote shifts from crossing contest boundaries, instead silently converting them to undervotes. Without this subversion, shifted Biden votes should have been assigned to Natural Law Party presidential candidate Rocky De La Fuente, creating an obvious artifact of fraud.
B. Barry County Corroboration
Evidence from Barry County, Michigan provided real-world corroboration of the EMS subversion theory. Jada Chadwick, a Barry County resident, submitted a notarized affidavit with photographic evidence showing that at 11:17 PM on November 3, 2020, election night reporting displayed:
- Rocky De La Fuente: 8,883 votes (39.4%)
- Trump: 8,744 votes (38.8%)
- Biden: 4,675 votes (20.7%)
- 41% of precincts reporting
De La Fuente’s official final count in Barry County was 16 votes.
Lenberg concluded: “This type of aberration occurring during a live election is consistent with a subversion being employed operationally by a malicious actor in a misconfigured mode… In Barry County during election night November 3, 2020 it is apparent that the subversion was misconfigured resulting in the shifting of votes and consequently causing votes to accrue to the Natural Law Party Candidate, Rocky De La Fuente”.
The analyst assessed that “a rapid deployment of a pre-planned software fix or an updated configuration” would have been required to correct this visible error, potentially deployed “across the State of Michigan on all Dominion Voting Systems EMS/RTR systems where the incomplete subversion had a similar malfunction”.
C. Unexplained Vote Discrepancies
Direct forensic analysis of compact flash cards revealed vote count discrepancies that could not be explained by the official narrative of human error. In Helena Township, Lenberg’s decryption and decoding of the actual results file from the compact flash card showed:
Straight Party ticket votes: Biden 136, Trump 254
Direct Presidential votes: Biden 217, Trump 306
Total votes recorded: Biden 353, Trump 560
Total votes in official November 21 EMS report: Biden 306, Trump 431
Discrepancy: 176 presidential votes (19.3% of votes cast) unaccounted for in the official report, with Biden reduced by 47 votes and Trump reduced by 129 votes.
IV. Ballot Handling and Tabulation Irregularities
A. Absence of Serial Numbers and Ballot Security
Forensic examination revealed that official ballots used in Antrim County contained no serial numbers, enabling unlimited re-scanning without detection. Lenberg stated: “This means that the same ballots can be fed multiple times into the tabulators without any detection or warnings that they have already been processed once before and that they are duplicate”.
The lack of serial numbers combined with other security deficiencies meant:
No detection capability for duplicate ballots
No tracking of individual ballot chain of custody
Easy fabrication of counterfeit ballots using consumer equipment
Ballot fabrication feasibility: Testing confirmed that ballots could be replicated for approximately $280 (large format printer) plus $50 (500 sheets of 11×17 heavyweight paper). Lenberg calculated: “In a night could make 12 ballots per minute (double sided) * 60 minutes * 12 hours > 8600 ballots”. With commercial printing equipment, “tens of thousands” could be produced overnight.
An ElectionSource whistleblower publicly stated in a video transcript that ElectionSource technicians carried thumb drives containing all ballot PDF images for the counties they serviced, and “there is no chain of custody when it comes to them… You know, back before we did mass mail in voting, nobody thought twice about shipping those digital ballots to the appropriate sources”.
B. Extreme Ballot Reversal Rates
Analysis of tabulator log files (slog.txt) from compact flash cards revealed abnormally high ballot reversal rates – instances where ballots were rejected by tabulators and returned to poll workers for reprocessing.
| Township/Event | Reversal Rate | Context |
|---|---|---|
| Central Lake (Nov 6, 2020 reprocessing) | 82% | 1,222 reversals out of 1,491 total votes |
| Warner Township Logic & Accuracy Testing (Oct 20, 2020) | 110% | 283 reversals during processing of 256 test ballots |
| Helena Township (Nov 3, 2020) | 21% | Disproportionately impacted Republicans 20% more than Democrats |
| Mancelona Township Precinct 1 (Nov 3, 2020) | 28.9% | Continuous feeding pattern after polls closed |
Physical evidence of ballot tampering: Forensic analysis of error logs showed specific outer marker blocks (15, 18, 28, 41, 44) on ballots were modified, causing reversals. Sample error messages from both Warner and Central Lake Townships showed identical patterns:
"error, left marker#18, rectangle height, detected 35, expected 24"
"failed correction, left edge marker#18, pattern match"
"error, left edge marker#18 on top side not found"
"Ballot format or id is unrecognizable"
Laboratory testing confirmed these errors could be replicated by manually adding marks to ballot outer markers with a pen, changing their shape.
Late-night ballot processing in Mancelona: Log analysis revealed that after individual in-person voting ceased at 8:33 PM on November 3, 2020, ballot processing continued with a methodical pattern – one ballot approximately every 11 seconds for nearly 4 hours, ending at 12:21 AM on November 4. This represented 313 ballots “processed in a methodologic fashion one right after another,” inconsistent with normal voter behavior.
C. Ballot PDF Design Flaws
Technical analysis of the official ballot PDF files stored on the EMS revealed design defects that would increase error rates:
- Asymmetric margins: Top of ballot had 15mm whitespace; bottom had only 5mm
- Vote target misalignment: Internal contest blocks shifted 1mm right; external markers shifted 1mm left
- Total offset: 2mm shift in a 4mm vote bullet area = 50% offset from proper target location
Testing demonstrated that ballots fed top-first had less than 1% reversal rate, while the same ballots fed bottom-first (as would occur with ballot box stuffing) had approximately 20% reversal rate. These flaws “are present in the PDFs themselves on the EMS, they are not an error of the printing company or whoever was responsible for making the ballot”.
V. ElectionSource Vendor Control and Access
A. Centralized Configuration Authority
ElectionSource, a third-party contractor, maintained supreme technical control over Michigan election systems. James Penrose documented that “ElectionSource technicians responsible for the creation and deployment of project files have supreme power in creating configurations that can be used to modify the votes in the EMS and the output of the tabulator paper tapes”.
The vendor’s access included:
- Creation of all election project files for Antrim County
- Setting of default passwords for all precincts statewide
- Access to master encryption keys via original database files
- Authority to make configuration changes affecting vote processing
- Physical possession of ballot PDF images for multiple counties
Version control failures: ElectionSource set the “DCF File Version Number” to the same value (“50401”) for both the September 29, 2020 and October 23, 2020 project file deployments, despite substantive changes between them. This lack of version control resulted in incompatible configurations being deployed across Antrim County.
Ignored warning prompts: EMS logs showed that on multiple occasions (September 18, September 23, October 5, 2020), ElectionSource technicians acknowledged prompts stating “All previously created and deployed election files will be unusable” but failed to conduct wholesale redeployment of compact flash cards countywide. From October 24 through November 2, 2020 – the crucial final days before the election – there were “no entries in the UserInfo log file, indicating that there were no attempts made by either ElectionSource to complete this compact flash card update process”.
B. Threats Against Independent Forensic Analysis
On January 4, 2021, ElectionSource sent a letter to Michigan county clerks warning that “any transfer of equipment or software to a third party would be in direct violation of the State of Michigan software license terms” and that “Election Source, the State or Dominion may take immediate legal action for such breach of contract”. This threatened legal action against clerks seeking to fulfill their statutory oath to “hold fair and accurate elections”.
VI. Missing Evidence and Audit Trail Gaps
A. Equipment Not Produced for Forensic Analysis
Despite court-ordered discovery, multiple critical system components listed in Antrim County’s purchase documents were never produced for examination:
- ImageCast Listener Express Server
- ImageCast Express Firewall
- EMS Express Managed Switch
- ICP Wireless Modems (17 units)
- ImageCast Communications Manager Server
- ImageCast Listener Express RAS (Remote Access Server)
- ImageCast USB Modems (5 units)
- Network flow data, router configurations, and logs
Cotton stated: “Without these additional items and system components it will be impossible to determine the extent of public/private communications and the extent to which the proven anonymous remote access to the voting system components may have impacted the Antrim EMS databases and election results”.
B. Absent Ballot Images and Log Files
Ballot images: None of the 38 compact flash cards examined contained ballot images, and no images were imported into the EMS. Cyber Ninjas noted: “Ballot images are a critical artifact and are essential for any type of system audit to determine how an electronic voting machine interpreted results and where it might be malfunctioning”. Vendor training materials clearly stated ballot images should be imported immediately after the election, but this was never done.
Windows security logs: The EMS failed to maintain Windows security event logs before November 4, 2020 due to retention policy settings. This prevented analysis of pre-election system access and activities during the critical period when election files were being prepared and deployed.
Auto-deleting telemetry: Analysts discovered that the Customer Experience Improvement Program (CEIP) was enabled on the EMS with logs set to automatically delete every 5 minutes. The CEIP appeared to be enabled by unknown third-party software rather than through routine Microsoft use, and the rapid log deletion prevented security analysis.
Michigan Secretary of State destruction order: A December 1, 2020 memorandum from the Michigan Bureau of Elections authorized release of voting equipment security, which would allow destruction of removable media. This occurred before comprehensive forensic analysis could be conducted in multiple counties.
C. Lack of User Accountability
Generic shared accounts made it “near impossible to determine who performed an action even if proper logging was in place”. The EMS database contained only six account names (Ben Smythe, John Smith, Ryan Smoth, MRO M01, Return Office Admin, MRESuper Admin) to account for all administrative activities, regardless of which actual human was using the system.
Lenberg documented that “the true identity of Ben Smythe is not attainable through forensics alone and in fact appears to be a strawman user shared by all with access to the EMS, not a real human”. Any user logging in with the EMSADMIN username and password would appear as “Ben Smythe” in log files, making individual accountability impossible.
VII. System Maintenance Failures
A. Outdated Security Patches
Analysis revealed that voting systems operated with years-old software and security definitions, leaving them “extremely vulnerable to unauthorized remote access and manipulation”:
Operating system patches:
- Antrim EMS last updated: April 10, 2019
- Patches applied were already 15 versions behind at time of installation
- 97+ critical Windows 10 security updates issued since 2016 installation – none applied
Antivirus definitions:
- Windows Defender last updated: July 16, 2016 (the OS installation date)
- Antivirus definitions NEVER updated after system installation
- Weekly antivirus updates available since 2016 – none applied
Cotton concluded: “This lack of security updating and basic cyber security practices has left these systems in an extremely vulnerable state to remote manipulation and hacking… The fact that these systems are in such a state of vulnerability, coupled with the obvious public and private internet access, calls the integrity of the voting systems into question and should have negated the system accreditation”.
B. Unencrypted Hard Drives
Contrary to published guidelines for sensitive systems, hard disks on the Antrim EMS were not encrypted. This failure “increases the vulnerability of the voter data and facilitates the ease of access to sensitive data for unauthorized users and should invalidate any accreditation of the system”.
VIII. Source Code Review and Networked Automation
A. Dominion Patent Capabilities
Analysis of Dominion Voting Systems Patent US 8,876,002B2 (dated November 4, 2014) revealed that Dominion machines support networked Pre-LAT (Logic and Accuracy Testing) mode with extensive automation:
- Remote poll opening via network
- Vote simulation scripts that can “simulate voting patterns on the machine even to the level of providing pre-canned scanned ballot images or PDF images of ballots with machine generated marks”
- Remote instruction of Pre-LAT activities including “interpreting vote simulation scripts and images, performing image calibration procedures”
- Ability to program election ballots from over the network
Penrose noted: “If any of the automated configuration and testing functionality implemented by Dominion were to be abused in a systematic fashion, modification of election outcomes would be trivial for an attacker”.
Significantly, no evidence of Pre-LAT test results was found on the Antrim County EMS, despite the system’s capability to perform and log such tests.
B. Escrow Source Code Never Reviewed
Michigan Election Code Section 168.797c requires vendors to place source code in third-party escrow accounts, with the Secretary of State authorized to access it “solely for the purpose of analyzing and testing the software”. Despite the documented security concerns, the escrowed source code for the Dominion system was never retrieved and reviewed to determine:
- The precise implementation of error handling routines
- Whether Pre-LAT scripts or related functionality was used
- The full extent of networked capabilities
- Whether hard-coded credentials or encryption weaknesses exist throughout the codebase
Penrose concluded: “The evidence of a subversion in the EMS/RTR is sufficient that an expert review of the source code for the EMS/RTR is warranted to determine the extent of the subversion and breadth of the configuration options available to the malicious actors that would employ it”.
IX Court Outcomes
In the final analysis, the case brought forward by Attorney Matt DePerno on behalf of his client, Bill Bailey, was dismissed not on the basis of the evidence presented, but rather on the basis that all of the remedies sought by the plaintiff had been satisfied by the defense including their request for a statewide audit.
- May 25, 2021: Circuit court dismissed claims as moot, ruling “there is no right” under Michigan law for the audit sought
- April 21, 2022: Michigan Court of Appeals affirmed dismissal, stating plaintiff “failed to allege any ‘clear and positive’ factual allegations” and “merely raised a series of questions about the election without making any specific factual allegations as required”
- December 9, 2022: Michigan Supreme Court refused to hear the case, with Justice David Viviano stating “there’s nothing in state law that says every voter has the right to conduct their own independent audit of election results”
Michigan Attorney General Dana Nessel characterized the decision as “the final word in this case on the legitimacy and accuracy of our elections” and called the claims “fraudulent” and designed to “undermine the electorate’s faith in our system”.
In contrast to the assertions made by the MI AG, Judge Kevin Elsenheimer was very clear in asserting that there were indeed issues with the conduct of the 2020 election in Antrim County.

Of course, the facts surrounding the investigations into the conduct of the 2020 election in Antrim County, MI have not stopped those complicit with the malfeasance observed from asserting that there was no evidence of election fraud.
Expert Analyses
This report is based upon the following analyses that were submitted as court exhibits by forensic experts Benjamin Cotton (Cy Fir), Jeffrey Lenberg, James Penrose, and Doug Logan (Cyber Ninjas):
[03] CyTech CyFir #1 [Taiwan Germany] [040821]
[04] Cyber Ninjas #1 [SQL Database Mgmt] [040921]
[05] Penrose #1 [Modems and Dedicated Networks] [040921]
[07] Penrose #2 [ElectionSource] [050221]
[10] Lenberg #3 [Subversion in Antrim County] [050921]
[11] Lenberg #4 [Vote Shifting in Barry County] [051521]
[14] Lenberg #6 [Presidential Vote Count] [051821]
[19] Lenberg #10 [Ballot Abnormalities] [060921]
Defense Analyses
The findings detailed above directly contradicted a March 26, 2021 report by J. Alex Halderman (University of Michigan computer science professor) commissioned by Michigan Secretary of State Jocelyn Benson. Penrose and Lenberg filed a joint assessment on June 23, 2021 documenting specific inaccuracies in Halderman’s conclusions:
Halderman’s position: Vote discrepancies were “attributed strictly to human error” with no security breaches involved.
Contradictory evidence identified by analysts:
- Halderman stated his explanation “entirely” accounts for the Antrim County discrepancy, predicting Biden votes should have shifted to Natural Law Party. Testing showed Biden votes actually became undervotes – behavior only possible with EMS subversion.
- Halderman claimed “the ‘irregularities’ in the Antrim County election were not caused by a security issue or breach of any type.” This ignores documented anonymous remote logins on November 5 and 17, 2020 with administrator privileges.
- Halderman’s analysis “entirely omitted the fact that there was an extremely high ballot reversal rate of 111% in Logic and Accuracy Testing in Warner Township on October 20, 2020” and the 82% reversal rate in Central Lake on November 6, 2020.
- Halderman made “no mention” of shared passwords, null passwords on administrative accounts, or the 31-day window for potential log alteration between the anonymous logins and forensic acquisition.
Halderman himself had previously documented “multiple severe security flaws” in Dominion systems in sealed testimony for unrelated Georgia litigation (Curling v. Raffensperger), though his Michigan analysis took a contrary position.
Halderman Declaration