Before we get to a discussion of the technical risks, the patent merits asking a few non-technical questions:
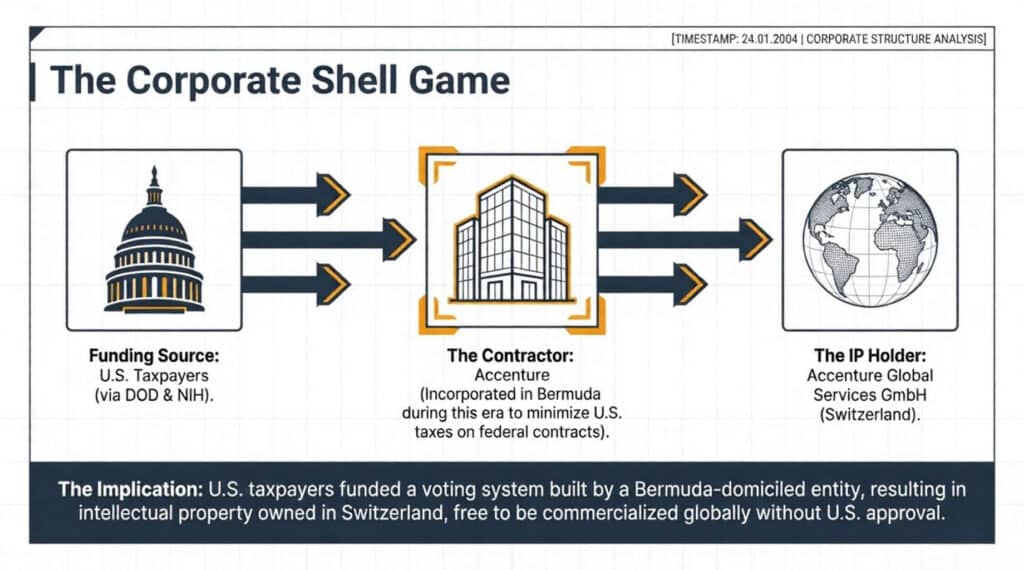
- Why is the National Institute for Health funding an election system patent for the Department of Defense?
- Why are U.S. taxpayer funds expended on behalf of assets owned by a foreign business…a business incorporated in Bermuda to avoid paying U.S. taxes?
- Why did inventors file patent paperwork AFTER the project that produced the invention was cancelled due to security vulnerabilities?
- What prevents “fake voters” from being injected for fraudulent purposes using this invention?
The potential answers to these questions alone should set off alarm bells about the intent of this invention. In fact, the volume of the alarm bells should be turned up a notch simply after reading the patent abstract.
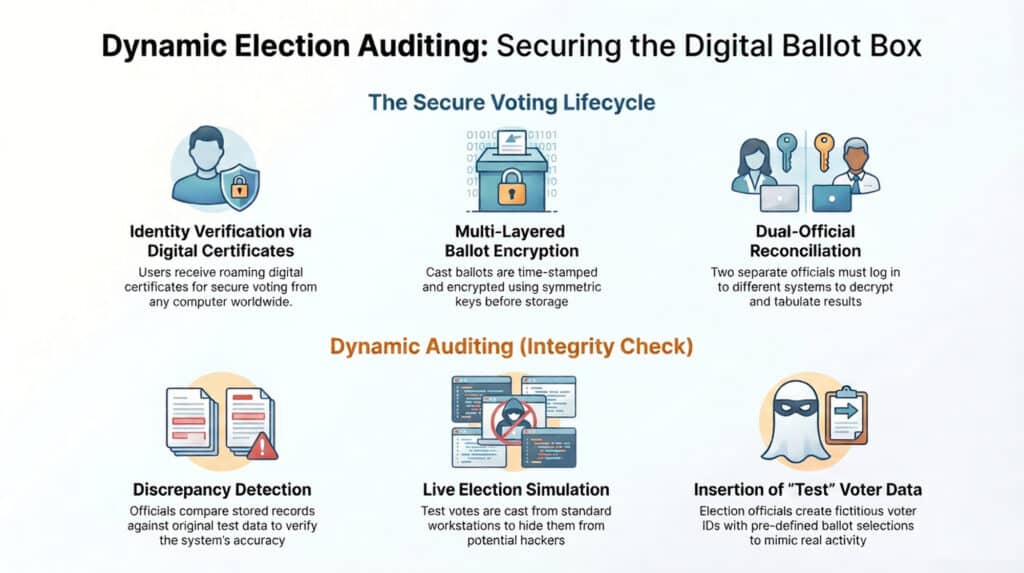
"The present invention relates to a system and method for dynamically auditing of electronic elections using an electronic registration and voting system. In particular, the present invention provides false voting data associated with false voters to the voting systems, recovers voting records associated with the false voters, and compares the stored voting records to the original false voting data."
Patent Abstract Tweet
The patent literally promotes the injection of “false voting data associated with false voters to the voting systems”. The inventors want us to believe that this “feature” actually enhances the security of internet-based voting systems.
United States Patent 7,549,049 Dynamic auditing of electronic elections
The core features of the invention are summarized in the following figure.
The Dynamic Election Auditing concept is riddled with security vulnerabilities. Let’s now look at the technical risks one attack vector at a time.
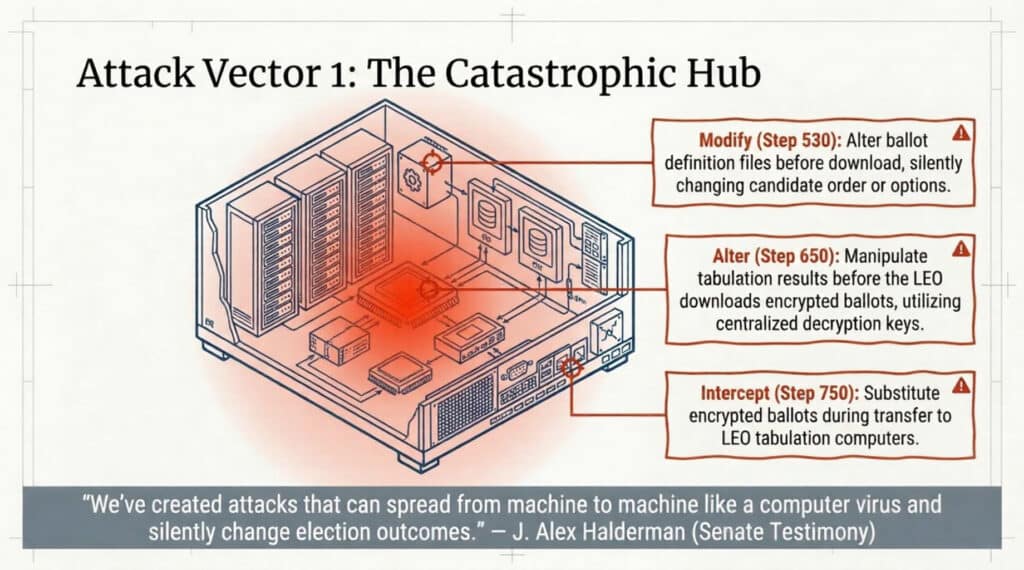
Attack Vector 1: The Catastrophic Hub
- Alter Tabulation: Change results before Local Election Offices (LEOs) download ballots, as the central server manages decryption keys.
- Modify Ballot Definitions: Silently change candidate order, remove candidates, or alter write-in options before voters download their ballots.
- Ballot Substitution: Intercept and replace encrypted ballots during transfer to LEO computers.
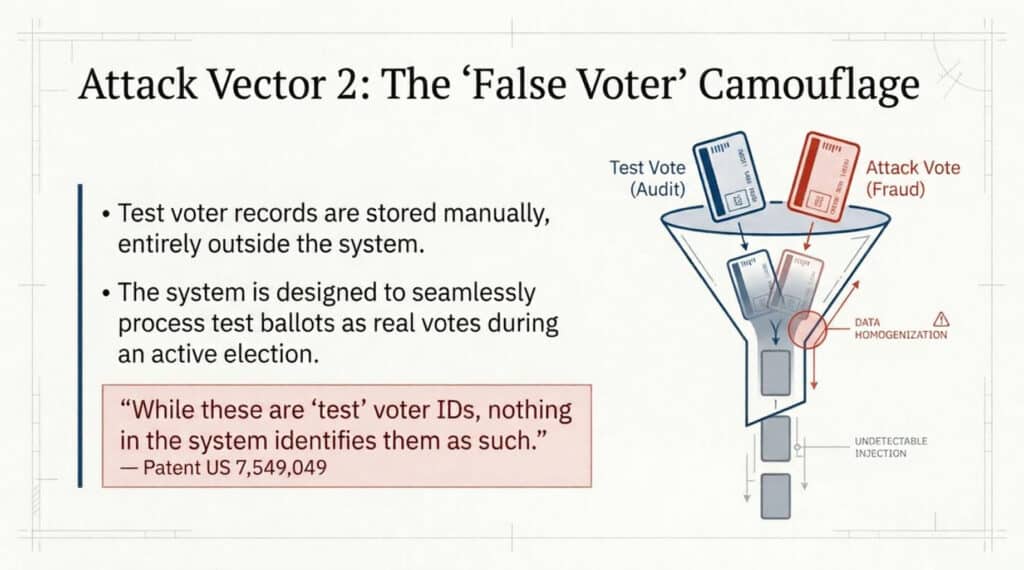
Attack Vector 2: The "False Voter" Camouflage
- Indistinguishable Fraud: Insiders can create fictitious voter IDs and inject pre-specified ballot choices into a live election.
- Lack of Systemic Audit: Test voter records are maintained manually and outside the system in election officials’ offices, leaving no digital audit trail to distinguish “legitimate” test injections from fraudulent ones.
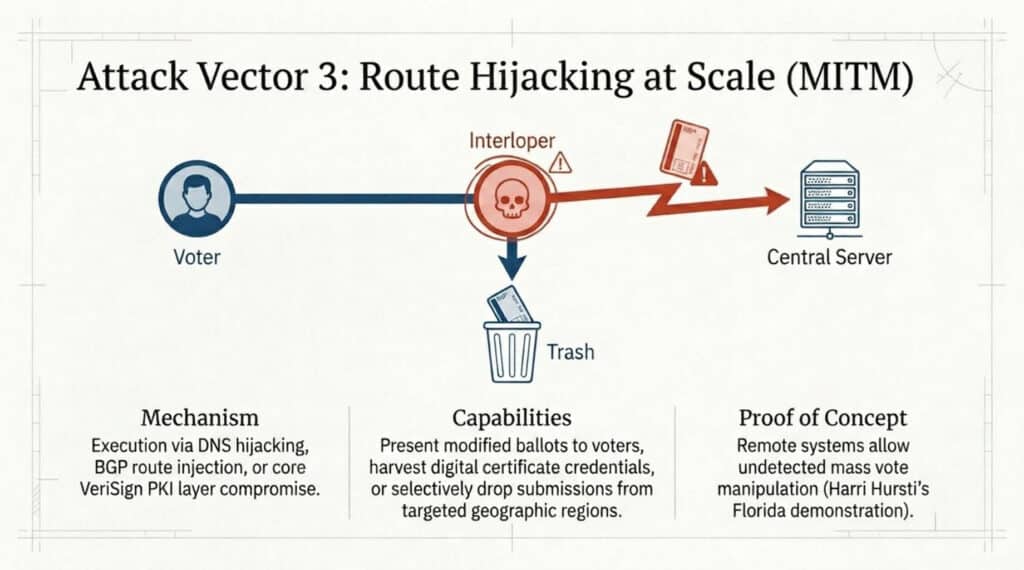
Attack Vector 3: Route Hijacking at Scale (MITM)
- Ballot Manipulation: Present voters with a modified ballot while submitting a different choice to the server.
- Credential Harvesting: Steal digital certificates for later unauthorized vote submission.
- Selective Suppression: Delay or drop ballot submissions from specific geographic regions based on predicted voting patterns.
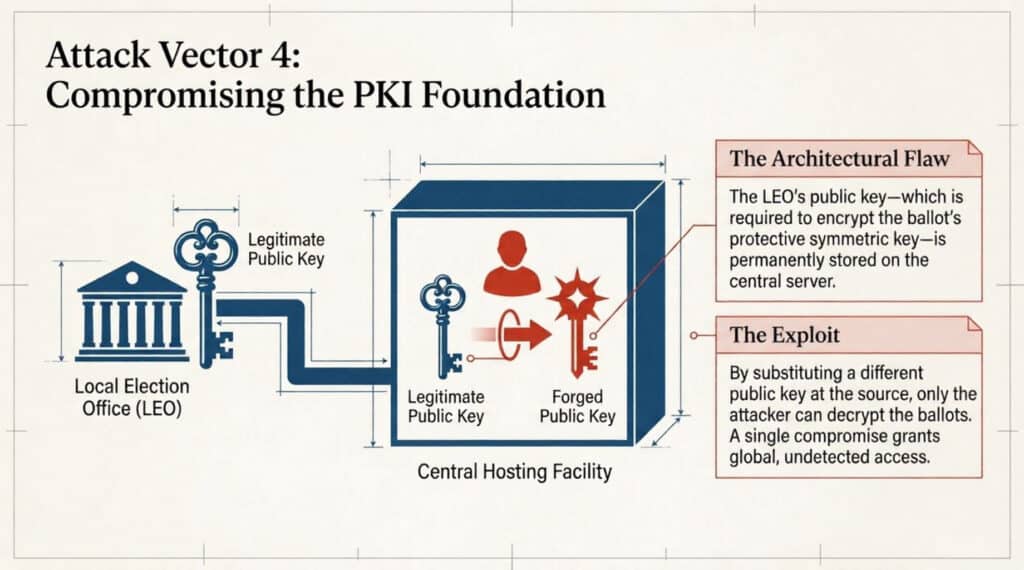
Attack Vector 4: Compromising the Public Key Infrastructure (PKI) Foundation
- Authority Compromise: If the PKI authority is coerced or compromised, fraudulent certificates can be issued to impersonate voters or officials.
- Key Substitution: The LEO’s public key is stored at the central facility; replacing it allows an attacker to become the only entity capable of decrypting ballots.
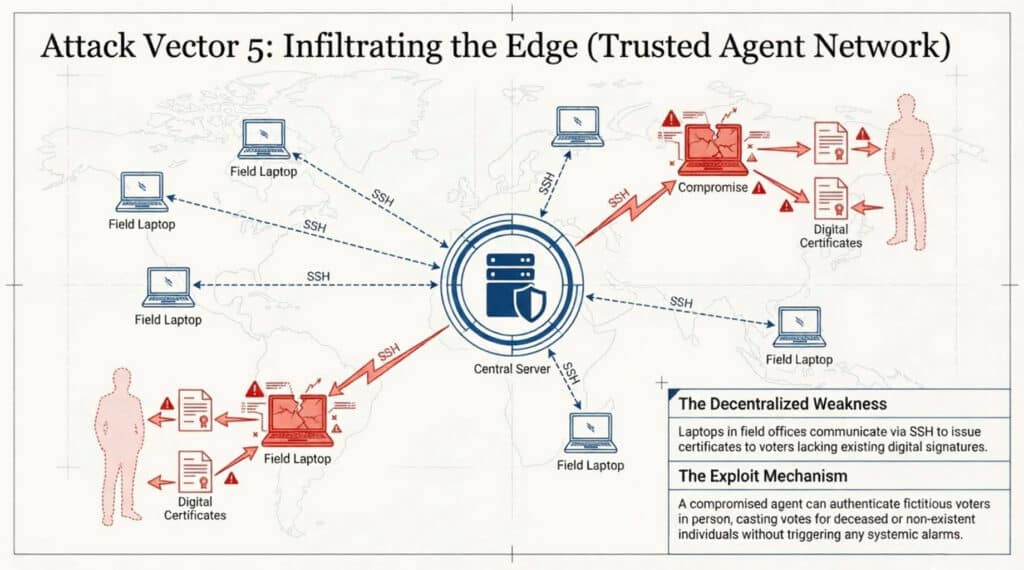
Attack Vector 5: Infiltrating the Edge (Trusted Agent Network)
- Vulnerability of Remote Nodes: These agents communicate via SSH from remote locations (e.g., field office laptops), which are significantly more vulnerable than hardened central servers.
- Fictitious Issuance: Fraudulent agents can issue certificates to non-existent or deceased individuals, enabling the casting of fraudulent votes.
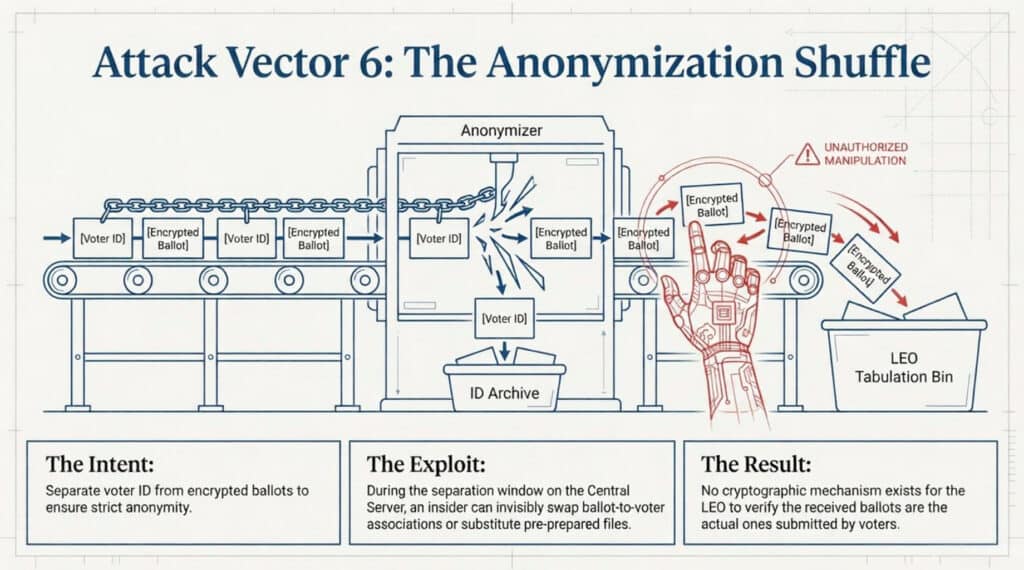
Attack Vector 6: The Anonymization Shuffle
- Association Swapping: During the separation window, an insider can link a voter’s choices to a different identity or substitute prepared encrypted files for legitimate ones.
- Verification Gap: Once shuffled, there is no cryptographic mechanism for an LEO to verify that the ballots received are the ones actually submitted by voters.
The "Legal Cover" Mechanism
In case the aforementioned attack vectors were not concerning enough, it is important to note that the dividing line between legitimate use and fraudulent abuse is almost non-existent. The patent’s provision for injecting false voting data for auditing purposes serves as a potent legal defense for manipulators. If an unauthorized injection is discovered, the actor could claim they were conducting legitimate audit testing under the patented methodology. The manual nature of test record-keeping makes it nearly impossible for forensic investigators to disprove such claims.
Chilling Similarities
The whistleblower testimony of a Senior Venezuelan Election Official asserts that elections in Venezuela were manipulated using what he referred to as a SAES data utility tool. The similarities between the SAES data utility tool described in his testimony and the dynamic auditing system in patent US7549049 are substantial, structurally parallel, and deeply alarming.
"This is supposed to be a tool that — for its normal usage, it's supposed to allow you to test the integrity of the system. When it's misused, it can allow you to inject votes without people knowing you did so." He further stated that during audits, "you will be auditing only that which the company wants you to see"
Senior Venezuelan Election Official Whistleblower Tweet
Both systems are explicitly described as testing/auditing tools that can emulate voting machines and inject data into live election infrastructure. The confidential witness testified that SAES data utility “allows you to test the entire electoral system” and “allows you to emulate voting machines in order to then transmit the votes”. Patent US7549049’s audit mechanism (FIG. 9 / Claim 19) operates identically — it injects “false voters with predefined ballots” into the live system and compares results. Both were designed for integrity verification; both can be weaponized to produce false votes undetected.
| Feature | SAES Data Utility (Testimony) | US7549049 Dynamic Audit (Patent) |
|---|---|---|
| Primary purpose | Test integrity of electoral system | Dynamically audit electronic elections |
| Mechanism | Emulates voting machines, transmits votes | Injects test voters with predefined ballots |
| Legitimate cover | System integrity testing | Audit mechanism |
| Abuse mode | Inject fictitious votes without detection | False voter injection indistinguishable from ballot stuffing |
| Audit evasion | Uses same system libraries to sign manipulated content | Test voters structurally identical to malicious injections |
| Detection difficulty | “Undetectable” — uses official system credentials | No anomaly threshold specified in any claim |
The book Stolen Elections by Ralph Pezzullo asserts that the SAES architecture featuring the SAES Data Utility is found in electronic voting systems used across America.
Conclusion
There are significant non-technical and technical risks with the Dynamic Auditing “invention” analyzed in this post. This technology reeks of a CIA tool that could be used to manipulate election outcomes. If this tool has been used to manipulate elections abroad, what prevents them or other entities to leverage commercialized versions of this technology to manipulate elections in the U.S.?