Patrick Byrne was among the first people to highlight how he has found evidence that one of the methods used to steal the 2020 election was via the use of what are called Virtual Machines installed within the Random Access Memory (RAM) found within the county Election Management System (EMS) servers. The “virtual machine in RAM” (VM-in-RAM) technique, as described by Patrick Byrne in his February 24, 2025, interview with National File, is an alleged method for manipulating vote tallies in Dominion Voting Systems’ EMS.
Byrne and others assert this was part of a broader foreign interference operation involving actors from Serbia and Chinese/Serbian military intelligence, uncovered during a March 2021 forensic investigation in Michigan led by attorney Stefanie Lambert. According to Byrne, the technique exploits the hardware’s memory to create temporary, ephemeral environments for altering data with minimal forensic traceability. He asserts it was one of over a dozen fraud mechanisms he funded probes into and that he possesses “100 percent of the evidence” to prove it.
Technical Definitions
Random Access Memory (RAM)
RAM is a type of computer memory that temporarily stores data your processor is actively using, so it can access that data very quickly. Unlike long-term storage (like a hard drive or SSD), RAM is volatile, which means its contents are lost when the power is turned off.
Virtual Machine
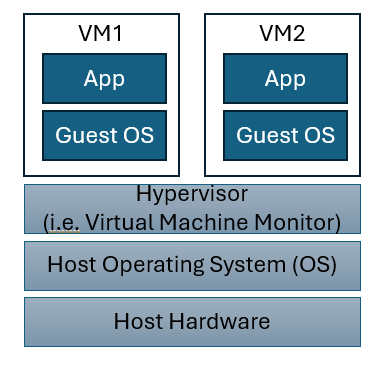
Virtual machines (VMs) are software-based computers that run on top of physical hardware, providing isolated, configurable environments for operating systems and applications. They are widely used for consolidation, testing, security isolation, and cloud computing.
Virtual machines have the following core features:
Virtual hardware: Each VM is given virtual CPU, RAM, disks, and network interfaces, mapped onto the host’s physical resources by a hypervisor.
- Hypervisor: A hypervisor is a software layer or system that enables multiple virtual machines (VMs) to run on a single physical computer by managing and allocating hardware resources such as CPU, memory, and storage between them. Hypervisors create isolated environments for each VM, ensuring they operate independently, even though they share the same physical host. This technology is fundamental to virtualization, allowing organizations to maximize hardware efficiency and flexibility, and is widely used in cloud computing and data centers.
Isolation: VMs are sandboxed from one another and from the host OS, so crashes or malware inside one VM do not directly affect others.
Guest OS independence: Each VM runs its own operating system (Windows, Linux, etc.), which can differ from the host and from other VMs.
VM in RAM Election Theft Method
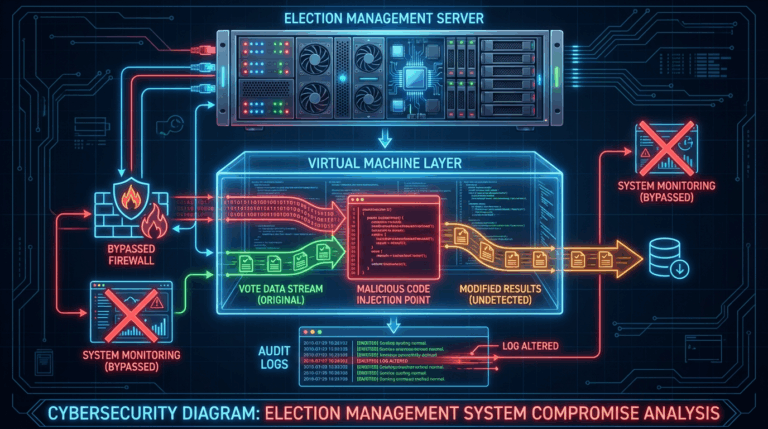
Byrne’s description portrays the VM-in-RAM method as a sophisticated, post-polls-closure hack that leverages the volatile nature of RAM (Random Access Memory) to avoid persistent logs. Here’s how he outlines it:
- Foreign operatives (allegedly from Serbia, with ties to Chinese intelligence) gain remote access to Dominion’s Election Management System (EMS) servers or county-level hardware via VPNs (Virtual Private Networks) or compromised credentials.
- This access is facilitated by prior infiltration, such as stealing encryption keys from Dominion’s QNAP NAS devices using malware like QSnatch (a real vulnerability Byrne referenced from 2020). Byrne claims IP traffic data, captured by an anonymous Japanese blogger and acquired by his network for $20 in Bitcoin, showed anomalous routing through Serbian and Hong Kong servers on Election Day 2020.
- After polls close, attackers load a lightweight virtual machine (VM) directly into the server’s RAM. Unlike traditional VMs stored on disk (e.g., via software like VMware), this is an in-memory instance—essentially a sandboxed operating environment booted from injected code.
- The VM runs in the EMS hardware’s volatile memory, allowing attackers to spin up a temporary election management system. Byrne describes it as “creating within the county election boxes a virtual machine within the RAM,” where they can access and modify vote databases without touching the physical storage drives.
- Tools like memory compilers or bootloaders (e.g., GRUB variants adapted for RAM execution) enable this, per Byrne’s network’s forensics. It exploits Dominion’s alleged architectural flaws, such as unsecured USB ports (vDrives) or removable memory cards used for ballot programming, which could propagate malware across machines.
- Inside the RAM-based VM, attackers allegedly run custom scripts or malware to flip votes. Byrne ties this to broader vulnerabilities, including:
- Algorithmic Flipping: Modifying the “minimum number of votes necessary” to favor a candidate (e.g., ensuring a 51% margin) while preserving statistical plausibility.
- Log Tampering: The malware alters audit logs, protective counters, and vote records in real-time. Even forensic tools would show “nothing amiss” because all changes occur in memory and sync back to storage seamlessly.
- This mirrors demonstrations in hacked voting systems (e.g., Princeton University’s 2006 Diebold analysis, which Byrne echoes), where malware inspects ballots and shifts votes silently. In 2020 context, Byrne claims it targeted swing states like Michigan, Georgia, and Pennsylvania.
- Once alterations are complete, the VM is terminated—wiped from RAM by rebooting the hardware or flushing memory. Since RAM is volatile (losing data on power loss), no files remain on disk.
- Traces are minimal: Potential artifacts include temporary network logs (e.g., VPN connections) or slight memory dumps if captured mid-process. Byrne says only “advanced forensics” on live traffic (like the IP data his team obtained) can detect it, as standard post-election audits focus on storage, not ephemeral memory states.
- He warns this leaves “almost no record,” making it “plausible deniability” for perpetrators.
Counterarguments and Debunking
Argument: While RAM-based VMs are possible (e.g., via tools like Firecracker or QEMU in memory), election hardware like Dominion’s is air-gapped (no internet) and audited for such exploits. Experts note that rebooting wipes RAM but would disrupt certification processes, leaving detectable gaps.
Rebuttal: There is a significant body of evidence including internal Dominion emails that provide evidence that the electronic voting systems, particularly the EMS servers featured in the VM in RAM attack method, were indeed connected to the internet. Furthermore, few, if any, election officials analyze configured systems for “certification gaps”.
Assertion: Dominion’s lawsuit argues Byrne’s claims are “inherently improbable” and rely on manufactured evidence. Courts have upheld the suit, disqualifying Lambert (Byrne’s lawyer) in August 2024 for “egregious misconduct” in leaking documents.
Rebuttal: The evidence was not “manufactured”. In fact, the validity of the evidence cited was verified by Dominion itself during the Dominion v Byrne court proceedings. What Dominion and its allies assert as “egregious misconduct” was the fact that attorney Stefanie Lambert shared evidence of criminal misconduct with law enforcement, Barry County, MI Sheriff Dar Leaf. Sheriff Leaf proceeded to share the information provided online as it dispelled many of the false assertions made by Dominion employees. This evidence can be viewed on Sheriff Leaf’s X Feed.
Assertion: Multiple 2020 audits (e.g., Georgia’s hand recount) and federal probes found zero evidence of widespread fraud. Byrne’s “100% proof” has not been publicly released or validated.
Rebuttal: What election officials assert as “audits” were typically merely “recounts”. The VM in RAM attack method is designed not to be detected. The only way to detect the use of this method is via a forensic examination of the affected systems. Antrim County, MI was one of the handful of places where this examination was allowed to proceed. The subsequent analysis by cyber experts is what revealed evidence of the VM in RAM attack vector.
Evidence Cited by Byrne
There are multiple sources of evidence cited by Patrick Byrne in support of his VM in RAM attack method assertions.
- Forensic Probe: Stemming from Antrim County, Michigan’s 2020 tabulation errors, Lambert’s team allegedly found “remnants of an enormous hack” in EMS hardware, including compiler remnants and VPN artifacts.
- Traffic Data: The Japanese blogger’s dataset showed U.S. Dominion IPs routing to foreign servers, used to “substantiate claims of foreign interference.”
- Related Vulnerabilities: Byrne references CISA’s 2022 report on Dominion flaws (e.g., nine “severe” issues allowing malware injection) and a 2006 academic paper on vote-stealing malware that spreads via memory cards.
Man in the Middle Attack
In Patrick Byrne’s description of the 2020 VM-in-RAM attack, the virtual machine effectively functions as a trusted Man-in-the-Middle (MitM) between the real Election Management System (EMS) software and the underlying database/hardware — but with a critical twist that makes it far more dangerous and stealthy than a classic network MitM.
Here is exactly how Byrne and the forensic people in his circle describe the MitM role of the RAM-based VM:
Classic Network MitM | VM-in-RAM MitM (as alleged) | Why it’s worse |
Sits on the wire or VPN, intercepting packets between tabulator and EMS server | Sits entirely inside the legitimate EMS server, inside its own RAM, masquerading as the legitimate Dominion EMS process | No network traffic to capture; looks 100 % like normal internal memory activity |
Requires ARP spoofing, DNS poisoning, or compromised router | Injected via stolen credentials, QSnatch malware on the QNAP NAS, or infected USB “vDrive” memory cards that Dominion techs plug in | Uses Dominion’s own authorized update paths |
Can be detected by packet inspection, TLS certificate mismatches, or latency | Intercepts database calls (SQL queries) directly in memory before they ever hit the disk or network stack | Bypasses every log that Dominion and auditors normally look at |
Usually read-only or limited flip capability | Has full read/write access to the live cast-vote-record (CVR) tables and audit logs while running | Can rewrite logs to match the flipped totals (“adjudication” entries, protective counters, etc.) |
Disappears when connection is torn down | Disappears automatically when the machine is rebooted or RAM is flushed — which happens normally after results are certified | Leaves little or no persistent forensic evidence |
How the “trusted” part works in their scenario
- The rogue VM is spawned from code that was already inside the legitimate Dominion ImageCast or EMS process (injected months earlier via a signed update or infected USB).
- The moment the real EMS software issues an SQL query (“SELECT * FROM CastVoteRecords”), the rogue VM hooks the function call in memory and returns its own doctored result set instead of letting the real database driver execute.
- When the EMS writes updated totals or adjudication records, the VM intercepts the INSERT/UPDATE statements, alters the numbers in flight, and then writes both the falsified record and a matching falsified log entry.
- To every other process on the machine (and to any human looking at the screen), everything appears perfectly normal because the VM is presenting itself as the trusted Dominion process. Once the VM is running in RAM, it is indistinguishable from the legitimate software to the operating system itself.
This attack vector resembles another real-world precedent. It is very similar to the technique used in advanced banking trojans (e.g., TrickBot, Emotet, or the Carbanak VM-based variants) that spin up virtualized versions of the banking app entirely in memory to intercept transactions without touching disk.
Dominion and independent cybersecurity experts (CrowdStrike, Mandiant, CISA, etc.) flatly deny that anything like this occurred or is even feasible on air-gapped, certified election equipment. Byrne’s side counters that the machines are not truly air-gapped (QNAP NAS devices were internet-connected in many counties) and that the necessary hooks were delivered via legitimate-seeming firmware/update packages.
Summary
The RAM-resident VM can be described as the ultimate trusted MitM attack because it sits between the election software and its own database on the very machine everyone trusts. There is a significant body of evidence in support of the assertion that this method was used to manipulate the 2020 election results. Perhaps the most significant evidence in support of the validity of this assertion is there are indications that the theft of the 2024 election was prevented using many of the machine vulnerabilities that “experts” say don’t exist.
Related Posts