On June 1, 2007, Venezuelan representatives of Smartmatic reached out Sequoia representatives to provide guidance on how to deploy a “certified trusted image” of its election system onto Sequoia systems. It’s one simply email, but it tells a very interesting story if you know what to look for.
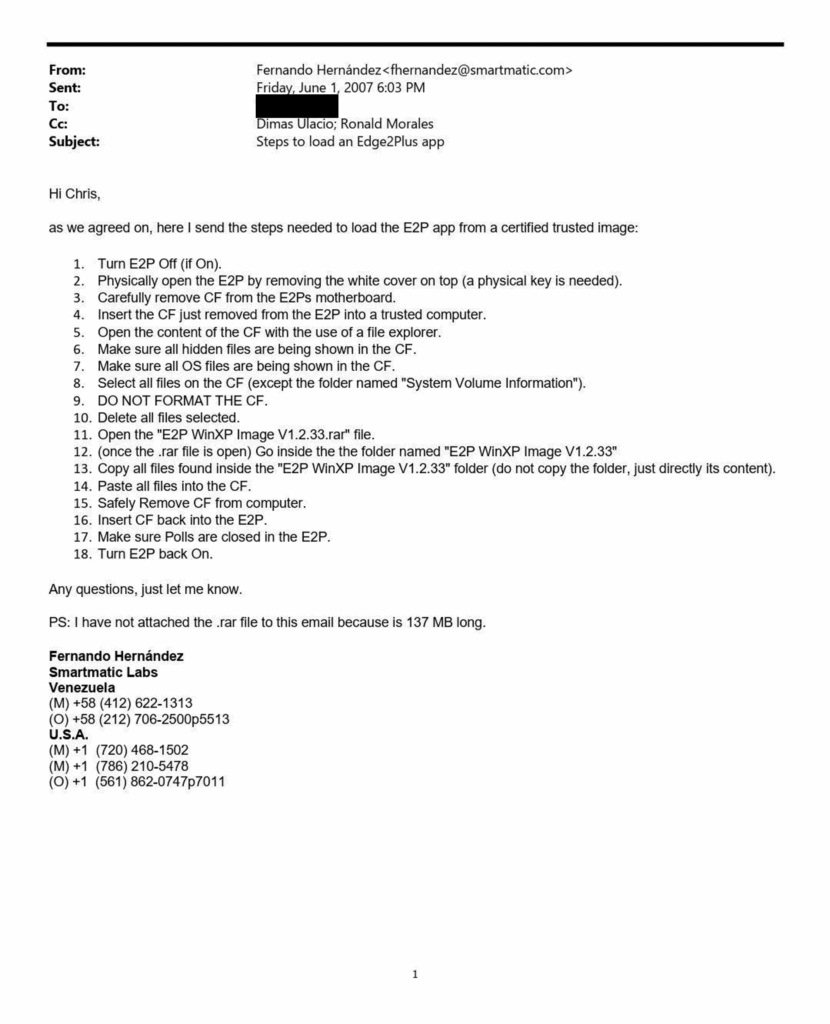
For starters, please note that Smartmatic acquired Sequoia on March 8, 2005 and remained its owner until November 2007. At that time, a group of U.S.-based investors organized as SVS Holdings, Inc. led by Sequoia President & CEO Jack Blaine and Chief Financial Officer Peter McManemy purchased Sequoia in the wake of a 2006 CFIUS investigation into foreign ownership of a U.S. election system company. Dominion Voting System later acquired Sequoia in 2010.
The email indicates close technical coordination between Smartmatic technical representatives in Venezuela and U.S.-based Sequoia technical representatives. It also indicates the flow of certified build from Smartmatic to Sequoia and not the other way around. This indicates that Venezuela was the source of the software that was to be used in the conduct of U.S. elections. These assets were subsequently owned and likely deployed by Dominion Voting Systems in support of U.S. elections. This is the first and most significant security concern evident from this email. There are many others.
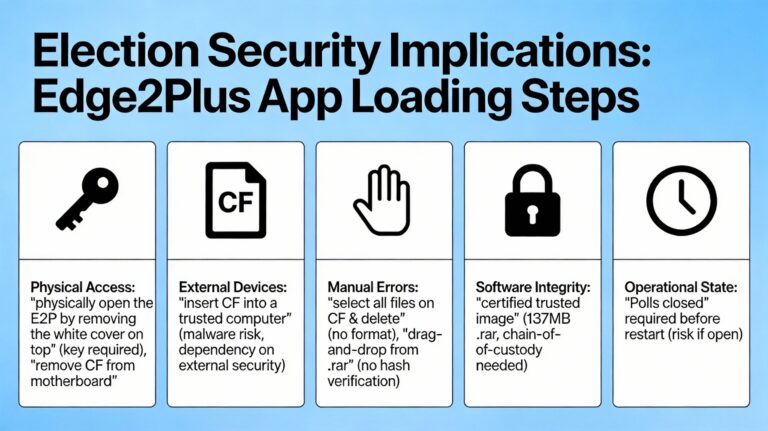
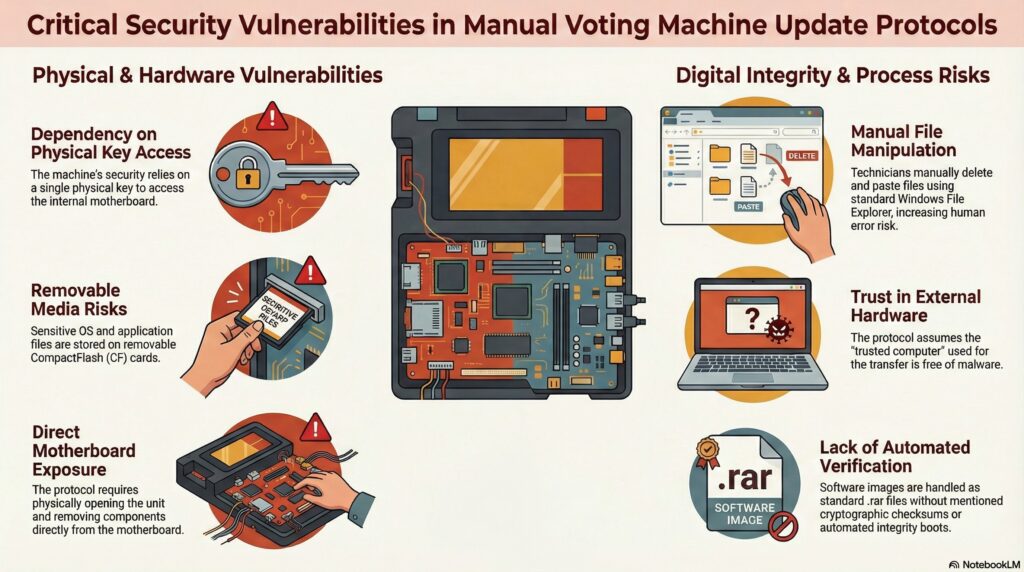
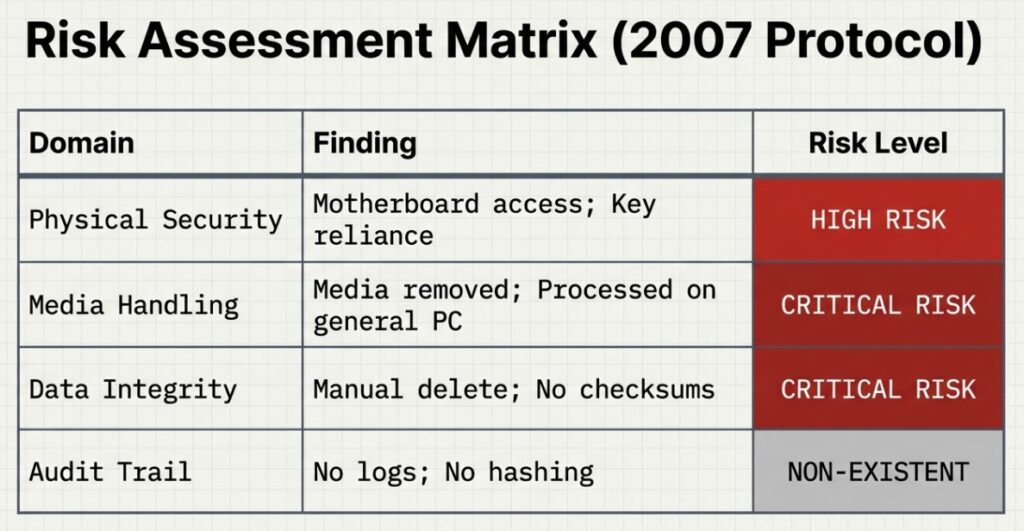
- Malware Propagation: By removing the storage media from the voting machine and connecting it to a general-purpose computer (even one designated as “trusted”), there is a risk that malware or viruses from the computer could infect the CF card before it is returned to the voting machine.
- Dependency on External Security: The integrity of the voting machine software becomes dependent on the security posture of the “trusted computer” used to perform the file transfer.
- Manual Deletion: The operator is instructed to “select all files on the CF” (ensuring hidden files are shown) and “delete all files selected”. The email explicitly warns “DO NOT FORMAT THE CF”. A mistake in this step—such as formatting the card or failing to delete specific files—could corrupt the storage media or the operating system.
- Manual Copying: The installation involves copying files from a compressed archive (“E2P WinXP Image V1.2.33.rar”) and pasting them directly onto the CF card. This manual “drag-and-drop” method lacks the automated verification checks (such as hashing or cryptographic signing verification during the install process) that are typically present in modern automated firmware installers.
.rar file that the sender notes was not attached due to size. The reliance on a file sent separately (presumably via internet transfer or removable media) necessitates strict chain-of-custody protocols to ensure the .rar file was not tampered with between the sender (Smartmatic Labs) and the recipient.Conclusion