On December 10, 2020, in the wake of the 2020 election, Dominion CEO John Poulos testified under oath with legal counsel present before the MI Senate Oversight committee that his voting systems were not connected to the internet.

Internal Dominion communications tell a much different story.
Electronic voting system vendors use the internet in many different ways including “sending election results”. For the purposes of this post, we examine their use of File Transfer Protocol (FTP) services.
How do electronic voting system manufacturers use FTP services?
FTP services are used support a variety of file transfers related to the deployment of election systems in support of our elections.
Internal emails show Dominion staff uploading and downloading full virtual machine (VM) images via FTP or managed file transfer (MFT) so remote engineers can connect to customer environments or test configurations. These images support VPN access and remote monitoring but are infrastructure and tooling, not voter records or cast-vote data.
Engineering communications reference Dominion-hosted FTP locations where partners and internal teams retrieve application packages, such as Android APKs and firmware-test tools, used to test ballot-printing devices and related components. These transfers involve software binaries and test jobs, not ballots, results databases, or voter registration files.
When customers need to send large sets of redacted ballot images or project materials to Dominion (for example, for audit or reporting tools like BARM), staff discuss using Dominion file-share or FTP/MFT infrastructure to move those image sets and associated outputs. The described workflow involves already-redacted images and results files used for certification and public posting, not live tabulation over FTP.
Security instructions direct developers to remove extra copies of source code from network and FTP locations and to inform management if any code remains stored there. This indicates that, where FTP is involved internally, it can also temporarily carry development artifacts such as source or build-related content, again separate from election-night transmission paths.
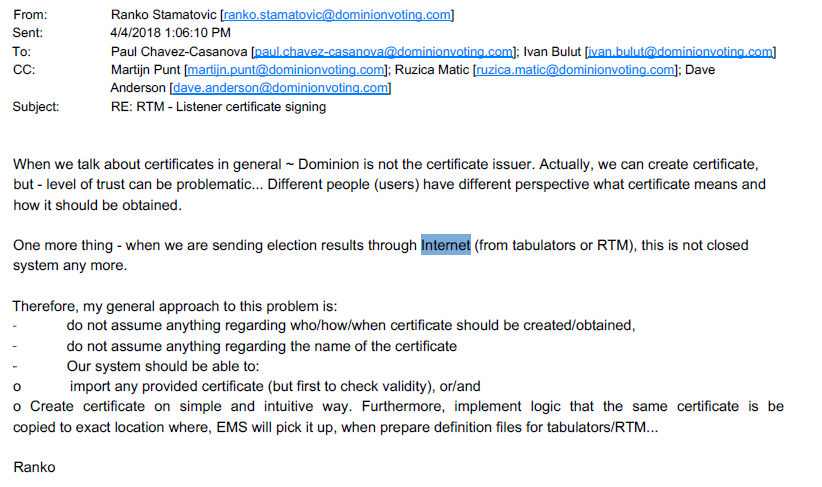
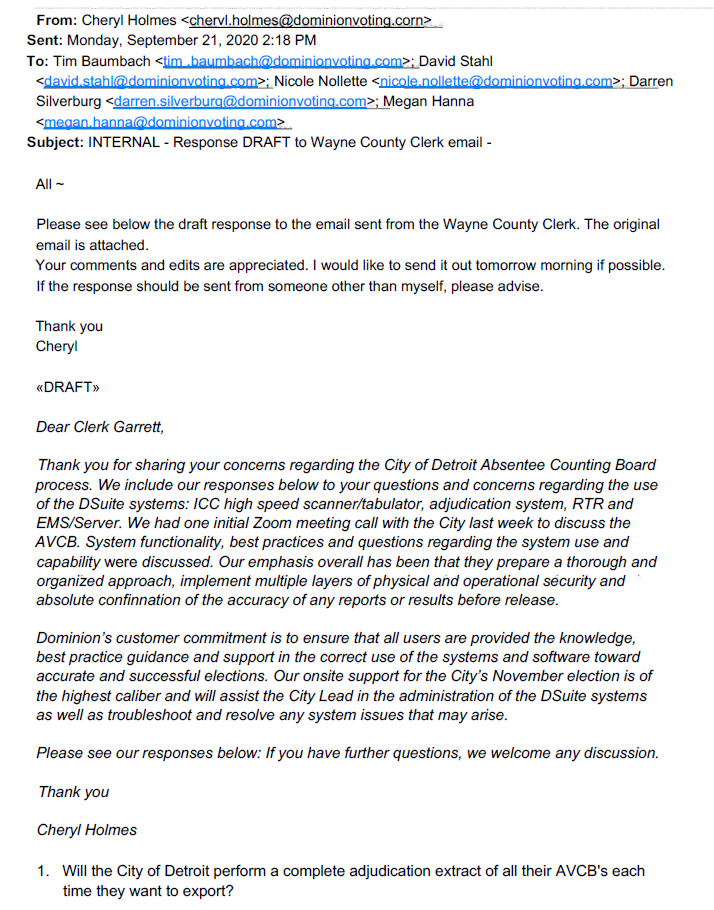
In the Detroit/Wayne County configuration, FTPS services are explicitly used as the mechanism for transferring election results files from the City to the County.
Direct evidence from the documents
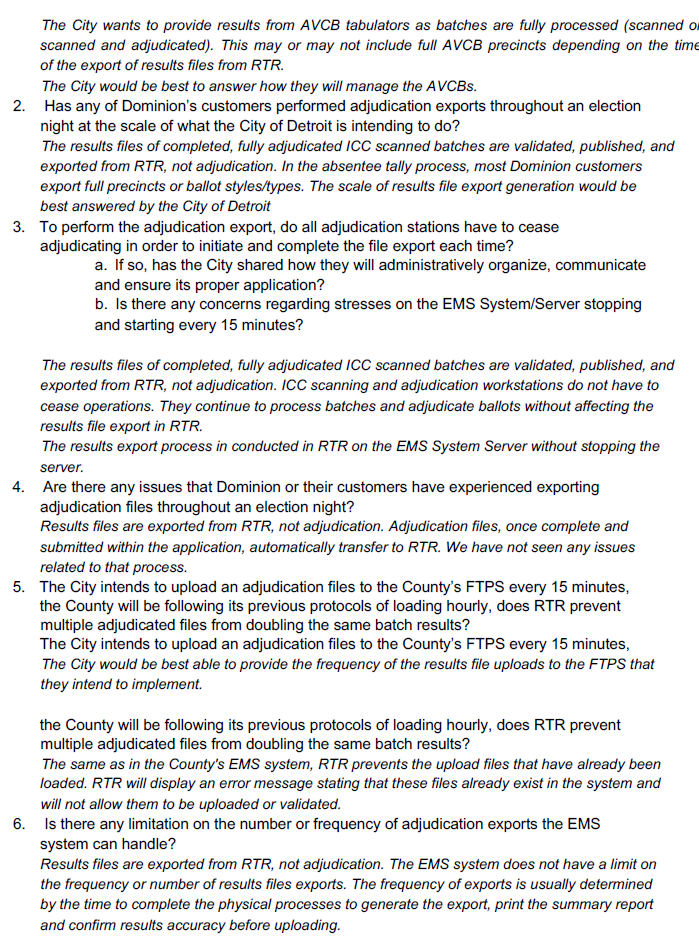
Dominion states that “the City intends to upload an adjudication file to the County’s FTPS every 15 minutes,” while “the County will be following its previous protocols of loading hourly,” confirming that the County receives results exports placed on its FTPS server by the City.
The same document clarifies that results files are generated and exported from RTR on the EMS system, then uploaded to “the County FTPS site” as part of the tally and reporting process for Detroit’s absentee counting boards.
Nature of the FTPS use
FTPS in this context is a secure file-transfer and staging service: the City posts RTR export files to the County’s FTPS server, and the County EMS/RTR later loads those files, with logic in RTR to prevent re‑loading duplicates.
FTP services use the internet
FTP and FTPS use the internet by running as application‑layer protocols over TCP/IP, establishing a control connection between client and server across routed IP networks, and then opening additional data connections to move files and directory listings.
Basic internet workflow
A remote client connects to the server’s public IP address and FTP/FTPS port (commonly 21 for control, with additional ports negotiated for data), with traffic routed over the internet like any other TCP connection.
After authentication, the client issues commands (such as listing directories, uploading, or downloading) over the control channel, while the actual file contents are sent over separate TCP data connections, which may be opened from server to client or client to server depending on active or passive mode.
Role of FTPS specifically
FTPS adds TLS/SSL on top of FTP, encrypting the control and/or data channels so that credentials and file contents cannot be read in transit over the public internet.
In practice, organizations expose an FTPS server on a public IP (often behind a firewall with port‑forwarding) and remote users or systems connect over the internet to securely exchange files, while the underlying routing and delivery are handled by standard IP infrastructure and TCP sessions.
Do FTP services pose any election security risks?
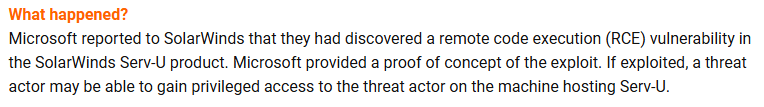
The short answer is “Yes”. We will examine the security risks of FTP services used by the two largest electronic voting system vendors in the United States – Dominion and ES&S. Dominion Voting Systems (now Liberty Vote) uses the Solarwinds Serv-U platform. ES&S uses the Progress Software MOVEit platform.
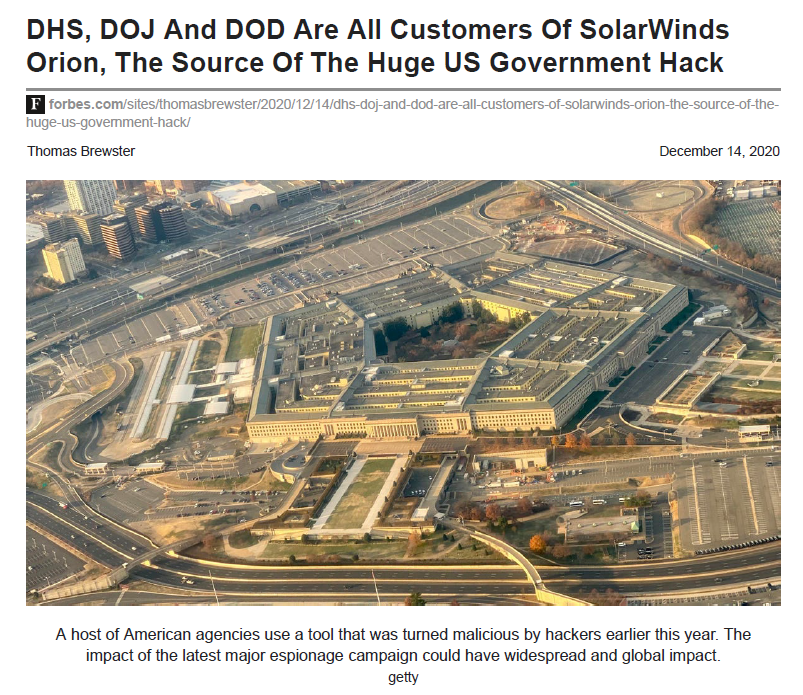
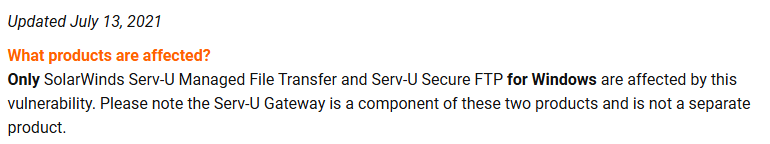
Solarwinds Serv-U Security Vulnerabilities
In December 2020, right after the 2020 general election, news broke to the public of a “huge” Solarwinds hack that affected 18,000 customers including the agency responsible for securing government networks – CISA.
On July 9, 2021, Solarwinds released a security advisory pertaining to their Serv-U FTP platforrm.
The Serv-U platform was used to transfer election results as evidenced by these communications between Wayne County, MI election officials and Dominion representatives.
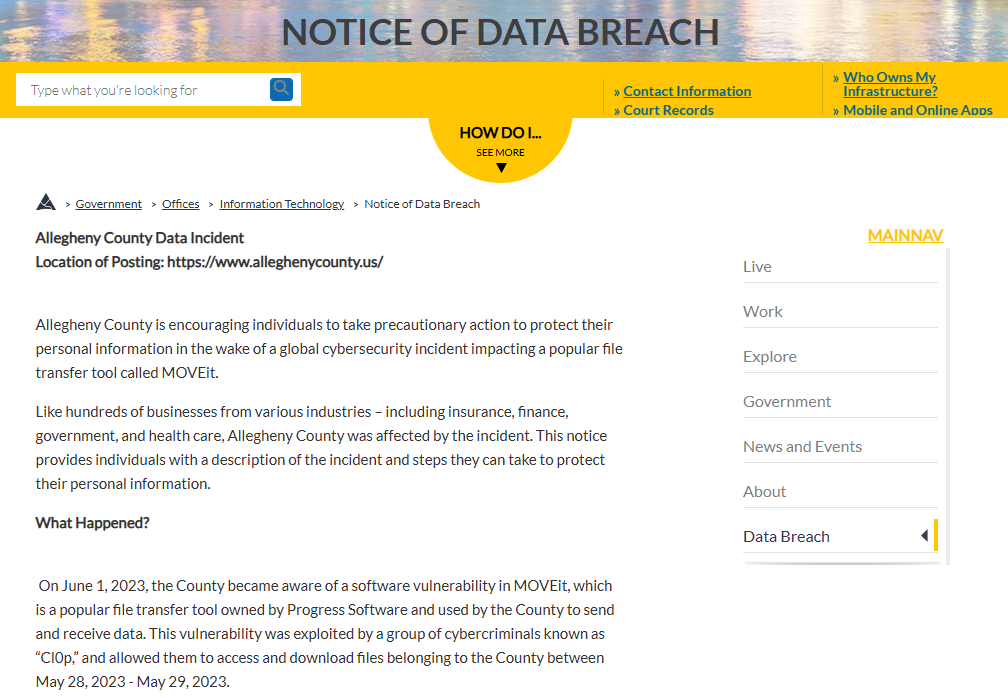
MOVEit Security Vulnerabilities
On June 1, 2023, the Allegheny County, PA became aware of a software vulnerability in MOVEit used by the County to send and receive data. This vulnerability was exploited by a group of cybercriminals known as “Cl0p,” and allowed them to access and download files belonging to the County between May 28, 2023 – May 29, 2023. These exploits may have been discovered in 2023, but there is no indication of how long the vulnerabilities exploited in 2023 may have been exploited by other “more discrete” actors.
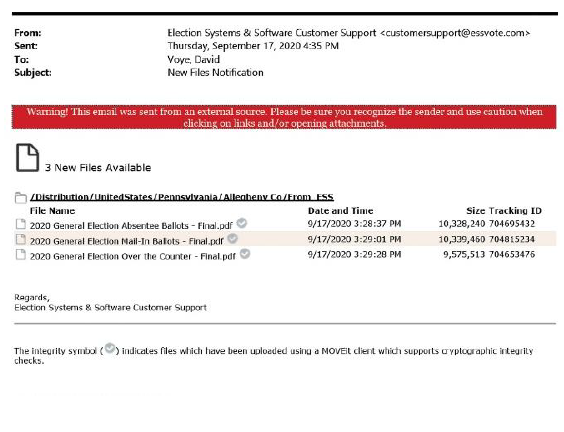
FOIA requests have revealed that the MOVEit FTP service was not only used in support of the 2020 election cycle but also during the 2023 election cycle.

Conclusion
The deployment of electronic voting systems in support of our elections leans heavily upon FTP services. These FTP services have proven security vulnerabilities that have been exploited. The utter lack of transparency in the chain of custody for the transfers of sensitive election records coupled with the misrepresentation of how these systems work by those trusted to deploy them should concern all Americans. Add the use of FTP services to the long list of reasons that America should no longer allow the use of electronic voting systems in the conduct of our elections.